- 联系我们
- duidaima.com 版权声明
- 闽ICP备2020021581号
-
 闽公网安备 35020302035485号
闽公网安备 35020302035485号
 闽公网安备 35020302035485号
闽公网安备 35020302035485号
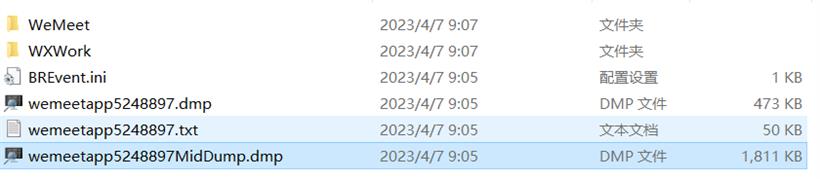
0:000> !analyze -v CONTEXT: (.ecxr) eax=008fdfe4 ebx=00000001 ecx=00000000 edx=2d692620 esi=3c4e1818 edi=3207f464 eip=1c5b34aa esp=008fe034 ebp=008fe094 iopl=0 nv up ei pl nz ac pe nc cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010216 meeting_dashboard_module+0x34aa: 1c5b34aa 8b01 mov eax,dword ptr [ecx] ds:002b:00000000=???????? Resetting default scope EXCEPTION_RECORD: (.exr -1) ExceptionAddress: 1c5b34aa (meeting_dashboard_module+0x000034aa) ExceptionCode: c0000005 (Access violation) ExceptionFlags: 00000000 NumberParameters: 2 Parameter[0]: 00000000 Parameter[1]: 00000000 Attempt to read from address 00000000 PROCESS_NAME: wemeetapp.exe READ_ADDRESS: 00000000 ERROR_CODE: (NTSTATUS) 0xc0000005 - 0x%p 0x%p %s EXCEPTION_CODE_STR: c0000005 EXCEPTION_PARAMETER1: 00000000 EXCEPTION_PARAMETER2: 00000000 STACK_TEXT: WARNING: Stack unwind information not available. Following frames may be wrong. 008fe094 7ad808f4 008fe320 00000000 ec0d8f9b meeting_dashboard_module+0x34aa 008fe214 7ad80617 008fe2f0 ec0d89ef 4ee246d8 desktop_common+0x108f4 008fe460 7ad7f4d7 776f6873 008fe400 79641fe1 desktop_common+0x10617 008fe5ec 7ad7ae62 008fe9d0 008fe76c 79bce43a desktop_common+0xf4d7 008fe5f8 79bce43a 008fe6b8 a0f1fbb4 326aed58 desktop_common+0xae62 008fe76c 7ad7de66 00000000 008fe9d0 ec0d8a63 wemeet_framework+0x2e43a 008fe7ec 7ad7deed 00000000 008fe9d0 008fe808 desktop_common+0xde66 008fe7fc 7ad7ae62 008fe9d0 008fe97c 79bce43a desktop_common+0xdee ...从上面的 ExceptionCode: c0000005 来看,这是一个经典的访问违例,从崩溃汇编的 mov eax,dword ptr [ecx] ds:002b:00000000=???????? 来看,当前的 ecx 中存放的是 0 ,从 0 上取内容自然就是访问违例。
要想知道访问违例的原因,就需要分析一下附近的汇编代码,用 .ecxr ; k 切到异常前的崩溃上下文。
# 堆代码 duidaima.com 0:000> .ecxr ; k eax=008fdfe4 ebx=00000001 ecx=00000000 edx=2d692620 esi=3c4e1818 edi=3207f464 eip=1c5b34aa esp=008fe034 ebp=008fe094 iopl=0 nv up ei pl nz ac pe nc cs=0023 ss=002b ds=002b es=002b fs=0053 gs=002b efl=00010216 meeting_dashboard_module+0x34aa: 1c5b34aa 8b01 mov eax,dword ptr [ecx] ds:002b:00000000=???????? *** Stack trace for last set context - .thread/.cxr resets it # ChildEBP RetAddr WARNING: Stack unwind information not available. Following frames may be wrong. 00 008fe094 7ad808f4 meeting_dashboard_module+0x34aa 01 008fe214 7ad80617 desktop_common+0x108f4 02 008fe460 7ad7f4d7 desktop_common+0x10617 03 008fe5ec 7ad7ae62 desktop_common+0xf4d7 04 008fe5f8 79bce43a desktop_common+0xae62 05 008fe76c 7ad7de66 wemeet_framework+0x2e43a 06 008fe7ec 7ad7deed desktop_common+0xde66 07 008fe7fc 7ad7ae62 desktop_common+0xdeed 08 008fe808 79bce43a desktop_common+0xae62 09 008fe97c 79bc784c wemeet_framework+0x2e43a 0a 008fe98c 79bc821f wemeet_framework+0x2784c 0b 008fe9a0 79bdac53 wemeet_framework+0x2821f 0c 008fea1c 79bdb791 wemeet_framework+0x3ac53 ...由于没有这些 dll 的符号,windbg 为了定义代码行数,就只能用 module + 0xxxxx 作为偏移来定位。
0:000> ub 1c5b34aa L20 meeting_dashboard_module+0x3449: 1c5b3449 00c6 add dh,al 1c5b344b 45 inc ebp 1c5b344c b000 mov al,0 1c5b344e e8cde2ffff call meeting_dashboard_module+0x1720 (1c5b1720) 1c5b3453 8d45b0 lea eax,[ebp-50h] 1c5b3456 c645fc04 mov byte ptr [ebp-4],4 1c5b345a 50 push eax 1c5b345b 8bce mov ecx,esi 1c5b345d ff15a8cb611c call dword ptr [meeting_dashboard_module+0x6cba8 (1c61cba8)] 1c5b3463 8d4db0 lea ecx,[ebp-50h] 1c5b3466 8945c8 mov dword ptr [ebp-38h],eax 1c5b3469 c645fc00 mov byte ptr [ebp-4],0 1c5b346d e8feebffff call meeting_dashboard_module+0x2070 (1c5b2070) 1c5b3472 51 push ecx 1c5b3473 8b4d0c mov ecx,dword ptr [ebp+0Ch] 1c5b3476 8bd4 mov edx,esp 1c5b3478 c7450c00000000 mov dword ptr [ebp+0Ch],0 1c5b347f 890a mov dword ptr [edx],ecx 1c5b3481 8bcf mov ecx,edi 1c5b3483 e8d8010000 call meeting_dashboard_module+0x3660 (1c5b3660) 1c5b3488 837dc801 cmp dword ptr [ebp-38h],1 1c5b348c 8b4f08 mov ecx,dword ptr [edi+8] 1c5b348f 8b01 mov eax,dword ptr [ecx] 1c5b3491 7509 jne meeting_dashboard_module+0x349c (1c5b349c) 1c5b3493 6a01 push 1 1c5b3495 6a01 push 1 1c5b3497 ff507c call dword ptr [eax+7Ch] 1c5b349a eb2b jmp meeting_dashboard_module+0x34c7 (1c5b34c7) 1c5b349c ff5048 call dword ptr [eax+48h] 1c5b349f 8bc8 mov ecx,eax 1c5b34a1 ff15ccc6611c call dword ptr [meeting_dashboard_module+0x6c6cc (1c61c6cc)] 1c5b34a7 8b4f08 mov ecx,dword ptr [edi+8] 1c5b34aa 8b01 mov eax,dword ptr [ecx] ...从汇编代码看,当前的 ecx 是来自于地址 edi+8,edi 的值有可能会在 meeting_dashboard_module+0x6c6cc (1c61c6cc) 方法中被修改,我们一并观察下。
0:000> dp @edi+8 L2
3207f46c ???????? ????????
0:000> u 1c61c6cc
meeting_dashboard_module+0x6c6cc:
1c61c6cc ?? ???
^ Memory access error in 'u 1c61c6cc'
我去,都是 ???,这表示当前的数据和机器指令都没有纳入到 dump 中,这也就是为什么 dump 小的原因。到这里好像就没法继续分析了,天要绝人之路吗?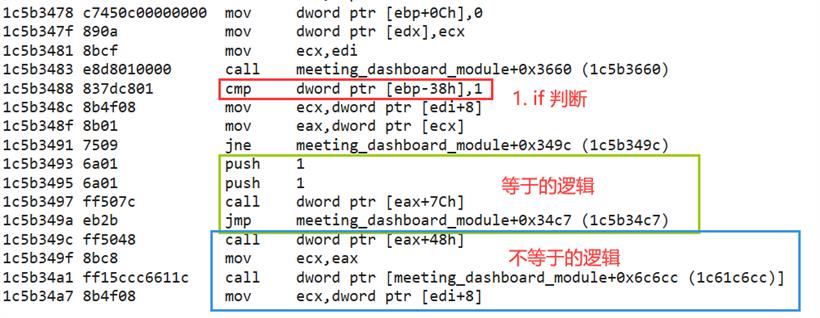
0:000> dp @ebp-38h L1 008fe05c 00000000那 @ebp-38h 是谁给的呢?继续观察汇编代码,发现是 meeting_dashboard_module+0x6cba8 函数的返回值 eax 给的 ,从汇编逻辑看, 0 是一种异常状态。
0:000> !teb
TEB at 0078a000
ExceptionList: 008fcf94
StackBase: 00900000
StackLimit: 008ee000
SubSystemTib: 00000000
FiberData: 00001e00
ArbitraryUserPointer: 00000000
Self: 0078a000
EnvironmentPointer: 00000000
ClientId: 00003ccc . 00004484
Real ClientId: 00000000 . 00000000
RpcHandle: 00000000
Tls Storage: 40a94180
PEB Address: 00787000
LastErrorValue: 18
LastStatusValue: 0
Count Owned Locks: 0
HardErrorMode: 0
这里的 18 是一个十进制,十六进制就是 0x12 ,那这个错误码代表什么意思呢?!error 已经不支持了,只能上 msdn 上找答案,截图如下: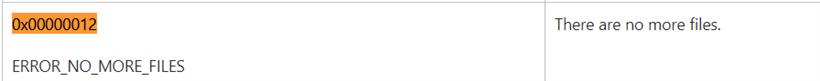
Solution 1 — Remove folder lock Solution 2 – Repair your registry Solution 3 — Run a full system scan Solution 4 — Update your OS Solution 5 — Remove recently installed software Solution 6 — Uninstall Comodo Cleaner/ ASUS security data manager Solution 7 — Boot into Safe Mode具体是什么原因,由于缺少符号再深入分析下去得要花一些时间了,这里就到此为止吧。